- Home
- > Hospitality
- > SANS Cybersecurity Exhibitors and Attendees List
SANS Cybersecurity Exhibitors and Attendees List
- 29 Mar - 03 Apr, 2026
- 2k - 5k Visitors
- Las Vegas, United States
SANS is a globally respected authority in cybersecurity education, professional training and industry-recognized certification. Its programs bring together cybersecurity practitioners, IT security teams, government agencies and enterprise professionals to build advanced skills in defending against modern cyber threats. Through hands-on learning and expert-led instruction, SANS helps organizations strengthen their security capabilities across critical areas such as incident response, digital forensics, cloud security and threat intelligence.
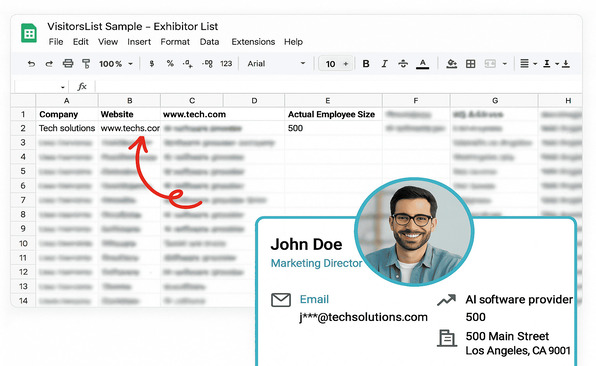
The SANS Exhibitors and Attendees List helps you reach cybersecurity professionals and security leaders investing in advanced training and security readiness. This audience includes decision-makers and technical specialists investing in advanced training, Certified programs and security technologies, making it an ideal resource for engaging qualified prospects focused on improving security readiness and workforce expertise.